
I’m a PhD researcher focused on the security of Blockchain and Cryptocurrency. Before academia, I spent 7 years in the military and finished as an army captain, which gave me some disciplined and hands-on experience. Now, I’m working on blockchain security at Tokamak Network, dealing with Layer 2 scalability and security issues. I also travel the world (mostly in Europe), and that really adds some fresh perspectives to my life. Outside of tech, I enjoy conversations about history, philosophy, jazz and science.
Current projects working on:
- Layer 2 security and cost analysis
- On-chain distributed randomness
latest posts
selected publications
2026
-

(Im)possibility of Incentive Design for Challenge-based Blockchain Protocols
In WTSC 2026 Workshop - 10th Workshop on Trusted Smart Contract, Mar 2026
Blockchains offer a decentralized and secure execution environment strong enough to host cryptocurrencies, but the state-replication model makes on-chain computation expensive. To avoid heavy on-chain workloads, systems like Truebit and optimistic rollups use challenge-based protocols, performing computations off-chain and invoking the chain only when challenged. This keeps normal-case costs low and, if at least one honest challenger exists, can catch fraud. What has been less clear is whether honest challengers are actually incentivized and a dishonest proposer is properly damaged under the worst case environment. We build a model with a colluding minority, heterogeneous costs, and three ordering modes. We then ask whether two goals can be met together: honest non-loss and fraud deterrence. Our results are clear: in single-winner designs, the incentive design is impossible or limited in scale. By contrast, in multi-winner designs, we obtain simple, explicit conditions under which both goals hold.
2025
-

Looking for Attention: Randomized Attention Test Design for Validator Monitoring in Optimistic Rollups
In arXiv preprint arXiv:2505.24393, Jun 2025
Optimistic Rollups (ORUs) significantly enhance blockchain scalability but inherently suffer from the verifier’s dilemma, particularly concerning validator attentiveness. Current systems lack mechanisms to proactively ensure validators are diligently monitoring L2 state transitions, creating a vulnerability where fraudulent states could be finalized. This paper introduces the Randomized Attention Test (RAT), a novel L1-based protocol designed to probabilistically challenge validators in ORUs, thereby verifying their liveness and computational readiness. Our game-theoretic analysis demonstrates that an Ideal Security Equilibrium, where all validators are attentive and proposers are honest, can be achieved with RAT. Notably, this equilibrium is attainable and stable with relatively low economic penalties (e.g., under $1000) for non-responsive validators and a low attention test frequency (e.g., under 1% per epoch). RAT thus provides a crucial, practical mechanism to enforce validator diligence, fortifying the overall security and integrity of ORU systems with minimizing additional costs.
2022
-
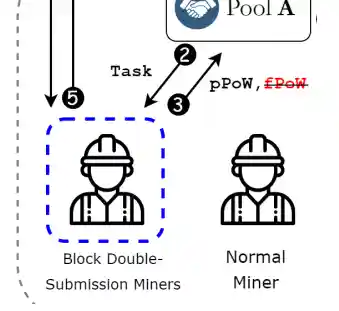
Block Double-Submission Attack: Block Withholding Can Be Self-Destructive
In AFT 2022 - ACM Conference on Advances in Financial Technologies, Jun 2022
Proof-of-Work (PoW) is a Sybil control mechanism adopted in blockchain-based cryptocurrencies. It prevents the attempt of malicious actors to manipulate distributed ledgers. Bitcoin has successfully suppressed double-spending by accepting the longest PoW chain. Nevertheless, PoW encountered several major security issues surrounding mining competition. One of them is a Block WithHolding (BWH) attack that can exploit a widespread and cooperative environment called a mining pool. This attack takes advantage of untrustworthy relationships between mining pools and participating agents. Moreover, detecting or responding to attacks is challenging due to the nature of mining pools. In this paper, however, we suggest that BWH attacks also have a comparable trust problem. Because a BWH attacker cannot have complete control over BWH agents, they can betray the belonging mining pool and seek further benefits by trading with victims. We prove that this betrayal is not only valid in all attack parameters but also provides double benefits; finally, it is the best strategy for BWH agents. Furthermore, our study implies that BWH attacks may encounter self-destruction of their own revenue, contrary to their intention.