Improper Restriction of Operations within the Bounds of a Memory Buffer (4.19.1)
Weakness ID: 119
Vulnerability Mapping: DISCOURAGED This CWE ID should not be used to map to real-world vulnerabilitiesAbstraction: Class Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
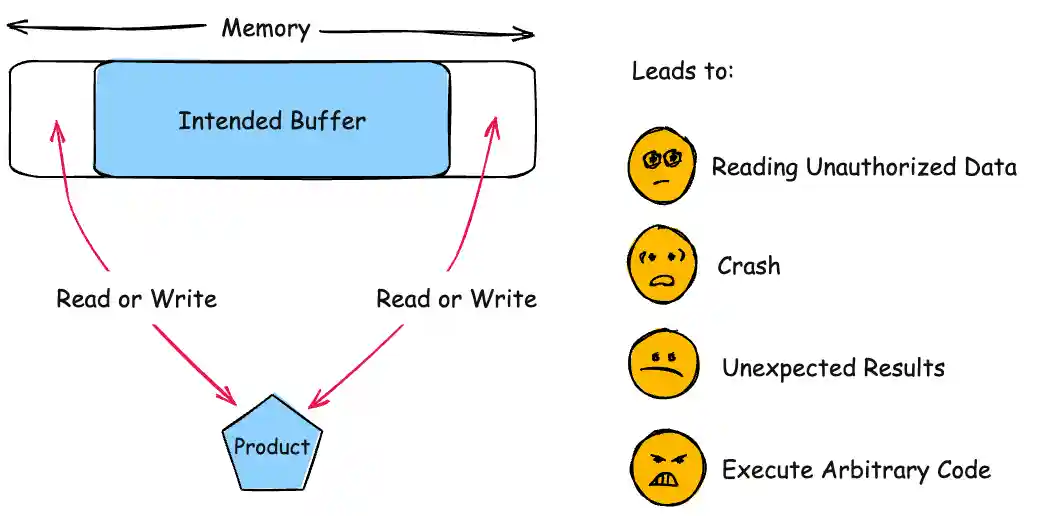
 Description
Description
 Alternate Terms
Alternate Terms
| Buffer Overflow |
This term has many different meanings to different audiences. From a CWE mapping perspective, this term should be avoided where possible. Some researchers, developers, and tools intend for it to mean "write past the end of a buffer," whereas others use the same term to mean "any read or write outside the boundaries of a buffer, whether before the beginning of the buffer or after the end of the buffer." Others could mean "any action after the end of a buffer, whether it is a read or write." Since the term is commonly used for exploitation and for vulnerabilities, it further confuses things. |
| buffer overrun |
Some prominent vendors and researchers use the term "buffer overrun," but most people use "buffer overflow." See the alternate term for "buffer overflow" for context. |
| memory safety |
Generally used for techniques that avoid weaknesses related to memory access, such as those identified by CWE-119 and its descendants. However, the term is not formal, and there is likely disagreement between practitioners as to which weaknesses are implicitly covered by the "memory safety" term. |
 Common Consequences
Common Consequences
 This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
| Impact | Details |
|---|---|
|
Execute Unauthorized Code or Commands; Modify Memory |
Scope: Integrity, Confidentiality, Availability
If the memory accessible by the attacker can be effectively controlled, it may be possible to execute arbitrary code, as with a standard buffer overflow. If the attacker can overwrite a pointer's worth of memory (usually 32 or 64 bits), they can alter the intended control flow by redirecting a function pointer to their own malicious code. Even when the attacker can only modify a single byte arbitrary code execution can be possible. Sometimes this is because the same problem can be exploited repeatedly to the same effect. Other times it is because the attacker can overwrite security-critical application-specific data -- such as a flag indicating whether the user is an administrator. |
|
Read Memory; DoS: Crash, Exit, or Restart; DoS: Resource Consumption (CPU); DoS: Resource Consumption (Memory) |
Scope: Availability, Confidentiality
Out of bounds memory access will very likely result in the corruption of relevant memory, and perhaps instructions, possibly leading to a crash. Other attacks leading to lack of availability are possible, including putting the program into an infinite loop. |
|
Read Memory |
Scope: Confidentiality
In the case of an out-of-bounds read, the attacker may have access to sensitive information. If the sensitive information contains system details, such as the current buffer's position in memory, this knowledge can be used to craft further attacks, possibly with more severe consequences. |
 Potential Mitigations
Potential Mitigations
| Phase(s) | Mitigation |
|---|---|
|
Requirements |
Strategy: Language Selection Use a language that does not allow this weakness to occur or provides constructs that make this weakness easier to avoid. For example, many languages that perform their own memory management, such as Java and Perl, are not subject to buffer overflows. Other languages, such as Ada and C#, typically provide overflow protection, but the protection can be disabled by the programmer. Be wary that a language's interface to native code may still be subject to overflows, even if the language itself is theoretically safe. |
|
Architecture and Design |
Strategy: Libraries or Frameworks Use a vetted library or framework that does not allow this weakness to occur or provides constructs that make this weakness easier to avoid. Examples include the Safe C String Library (SafeStr) by Messier and Viega [REF-57], and the Strsafe.h library from Microsoft [REF-56]. These libraries provide safer versions of overflow-prone string-handling functions. Note: This is not a complete solution, since many buffer overflows are not related to strings. |
|
Operation; Build and Compilation |
Strategy: Environment Hardening Use automatic buffer overflow detection mechanisms that are offered by certain compilers or compiler extensions. Examples include: the Microsoft Visual Studio /GS flag, Fedora/Red Hat FORTIFY_SOURCE GCC flag, StackGuard, and ProPolice, which provide various mechanisms including canary-based detection and range/index checking. D3-SFCV (Stack Frame Canary Validation) from D3FEND [REF-1334] discusses canary-based detection in detail. Effectiveness: Defense in Depth Note: This is not necessarily a complete solution, since these mechanisms only detect certain types of overflows. In addition, the result is still a denial of service, since the typical response is to exit the application. |
|
Implementation |
Consider adhering to the following rules when allocating and managing an application's memory:
|
|
Operation; Build and Compilation |
Strategy: Environment Hardening Run or compile the software using features or extensions that randomly arrange the positions of a program's executable and libraries in memory. Because this makes the addresses unpredictable, it can prevent an attacker from reliably jumping to exploitable code. Examples include Address Space Layout Randomization (ASLR) [REF-58] [REF-60] and Position-Independent Executables (PIE) [REF-64]. Imported modules may be similarly realigned if their default memory addresses conflict with other modules, in a process known as "rebasing" (for Windows) and "prelinking" (for Linux) [REF-1332] using randomly generated addresses. ASLR for libraries cannot be used in conjunction with prelink since it would require relocating the libraries at run-time, defeating the whole purpose of prelinking. For more information on these techniques see D3-SAOR (Segment Address Offset Randomization) from D3FEND [REF-1335]. Effectiveness: Defense in Depth Note: These techniques do not provide a complete solution. For instance, exploits frequently use a bug that discloses memory addresses in order to maximize reliability of code execution [REF-1337]. It has also been shown that a side-channel attack can bypass ASLR [REF-1333]. |
|
Operation |
Strategy: Environment Hardening Use a CPU and operating system that offers Data Execution Protection (using hardware NX or XD bits) or the equivalent techniques that simulate this feature in software, such as PaX [REF-60] [REF-61]. These techniques ensure that any instruction executed is exclusively at a memory address that is part of the code segment. For more information on these techniques see D3-PSEP (Process Segment Execution Prevention) from D3FEND [REF-1336]. Effectiveness: Defense in Depth Note: This is not a complete solution, since buffer overflows could be used to overwrite nearby variables to modify the software's state in dangerous ways. In addition, it cannot be used in cases in which self-modifying code is required. Finally, an attack could still cause a denial of service, since the typical response is to exit the application. |
|
Implementation |
Replace unbounded copy functions with analogous functions that support length arguments, such as strcpy with strncpy. Create these if they are not available. Effectiveness: Moderate Note: This approach is still susceptible to calculation errors, including issues such as off-by-one errors (CWE-193) and incorrectly calculating buffer lengths (CWE-131). |
 Relationships
Relationships
 This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
 Relevant to the view "Research Concepts" (View-1000)
Relevant to the view "Research Concepts" (View-1000)
| Nature | Type | ID | Name |
|---|---|---|---|
| ChildOf |
|
118 | Incorrect Access of Indexable Resource ('Range Error') |
| ParentOf |
|
125 | Out-of-bounds Read |
| ParentOf |
|
466 | Return of Pointer Value Outside of Expected Range |
| ParentOf |
|
786 | Access of Memory Location Before Start of Buffer |
| ParentOf |
|
787 | Out-of-bounds Write |
| ParentOf |
|
788 | Access of Memory Location After End of Buffer |
| ParentOf |
|
805 | Buffer Access with Incorrect Length Value |
| ParentOf |
|
822 | Untrusted Pointer Dereference |
| ParentOf |
|
823 | Use of Out-of-range Pointer Offset |
| ParentOf |
|
824 | Access of Uninitialized Pointer |
| ParentOf |
|
825 | Expired Pointer Dereference |
| CanFollow |
|
20 | Improper Input Validation |
| CanFollow |
|
128 | Wrap-around Error |
| CanFollow |
|
129 | Improper Validation of Array Index |
| CanFollow |
|
131 | Incorrect Calculation of Buffer Size |
| CanFollow |
|
190 | Integer Overflow or Wraparound |
| CanFollow |
|
193 | Off-by-one Error |
| CanFollow |
|
195 | Signed to Unsigned Conversion Error |
| CanFollow |
|
839 | Numeric Range Comparison Without Minimum Check |
| CanFollow |
|
843 | Access of Resource Using Incompatible Type ('Type Confusion') |
| CanFollow |
|
1257 | Improper Access Control Applied to Mirrored or Aliased Memory Regions |
| CanFollow |
|
1260 | Improper Handling of Overlap Between Protected Memory Ranges |
| CanFollow |
|
1339 | Insufficient Precision or Accuracy of a Real Number |
 Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
| Nature | Type | ID | Name |
|---|---|---|---|
| MemberOf |
|
1003 | Weaknesses for Simplified Mapping of Published Vulnerabilities |
| ParentOf |
|
120 | Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') |
| ParentOf |
|
125 | Out-of-bounds Read |
| ParentOf |
|
787 | Out-of-bounds Write |
| ParentOf |
|
824 | Access of Uninitialized Pointer |
 Relevant to the view "CISQ Quality Measures (2020)" (View-1305)
Relevant to the view "CISQ Quality Measures (2020)" (View-1305)
| Nature | Type | ID | Name |
|---|---|---|---|
| ParentOf |
|
125 | Out-of-bounds Read |
| ParentOf |
|
130 | Improper Handling of Length Parameter Inconsistency |
| ParentOf |
|
786 | Access of Memory Location Before Start of Buffer |
| ParentOf |
|
787 | Out-of-bounds Write |
| ParentOf |
|
788 | Access of Memory Location After End of Buffer |
| ParentOf |
|
805 | Buffer Access with Incorrect Length Value |
| ParentOf |
|
822 | Untrusted Pointer Dereference |
| ParentOf |
|
823 | Use of Out-of-range Pointer Offset |
| ParentOf |
|
824 | Access of Uninitialized Pointer |
| ParentOf |
|
825 | Expired Pointer Dereference |
 Relevant to the view "CISQ Data Protection Measures" (View-1340)
Relevant to the view "CISQ Data Protection Measures" (View-1340)
| Nature | Type | ID | Name |
|---|---|---|---|
| ParentOf |
|
123 | Write-what-where Condition |
| ParentOf |
|
125 | Out-of-bounds Read |
| ParentOf |
|
130 | Improper Handling of Length Parameter Inconsistency |
| ParentOf |
|
786 | Access of Memory Location Before Start of Buffer |
| ParentOf |
|
787 | Out-of-bounds Write |
| ParentOf |
|
788 | Access of Memory Location After End of Buffer |
| ParentOf |
|
805 | Buffer Access with Incorrect Length Value |
| ParentOf |
|
822 | Untrusted Pointer Dereference |
| ParentOf |
|
823 | Use of Out-of-range Pointer Offset |
| ParentOf |
|
824 | Access of Uninitialized Pointer |
| ParentOf |
|
825 | Expired Pointer Dereference |
 Relevant to the view "Seven Pernicious Kingdoms" (View-700)
Relevant to the view "Seven Pernicious Kingdoms" (View-700)
| Nature | Type | ID | Name |
|---|---|---|---|
| ChildOf |
|
20 | Improper Input Validation |
 Background Details
Background Details
 Modes
Of Introduction
Modes
Of Introduction
 The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
| Phase | Note |
|---|---|
| Implementation |
 Applicable Platforms
Applicable Platforms
 This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
| Languages |
Class: Memory-Unsafe (Often Prevalent) C (Often Prevalent) C++ (Often Prevalent) Class: Assembly (Undetermined Prevalence) |
| Technologies |
Class: Not Technology-Specific (Undetermined Prevalence) |
 Likelihood Of Exploit
Likelihood Of Exploit
 Demonstrative Examples
Demonstrative Examples
Example 1
This example takes an IP address from a user, verifies that it is well formed and then looks up the hostname and copies it into a buffer.
(bad code)
Example Language: C
void host_lookup(char *user_supplied_addr){
struct hostent *hp;
in_addr_t *addr;
char hostname[64];
in_addr_t inet_addr(const char *cp);
/*routine that ensures user_supplied_addr is in the right format for conversion */
validate_addr_form(user_supplied_addr);
addr = inet_addr(user_supplied_addr);
hp = gethostbyaddr( addr, sizeof(struct in_addr), AF_INET);
strcpy(hostname, hp->h_name);
}
This function allocates a buffer of 64 bytes to store the hostname, however there is no guarantee that the hostname will not be larger than 64 bytes. If an attacker specifies an address which resolves to a very large hostname, then the function may overwrite sensitive data or even relinquish control flow to the attacker.
Note that this example also contains an unchecked return value (CWE-252) that can lead to a NULL pointer dereference (CWE-476).
Example 2
This example applies an encoding procedure to an input string and stores it into a buffer.
(bad code)
Example Language: C
char * copy_input(char *user_supplied_string){
int i, dst_index;
char *dst_buf = (char*)malloc(4*sizeof(char) * MAX_SIZE);
if ( MAX_SIZE <= strlen(user_supplied_string) ){
die("user string too long, die evil hacker!");
}
dst_index = 0;
for ( i = 0; i < strlen(user_supplied_string); i++ ){
if( '&' == user_supplied_string[i] ){
dst_buf[dst_index++] = '&';
dst_buf[dst_index++] = 'a';
dst_buf[dst_index++] = 'm';
dst_buf[dst_index++] = 'p';
dst_buf[dst_index++] = ';';
}
else if ('<' == user_supplied_string[i] ){
/* encode to < */
}
else dst_buf[dst_index++] = user_supplied_string[i];
}
return dst_buf;
}
The programmer attempts to encode the ampersand character in the user-controlled string, however the length of the string is validated before the encoding procedure is applied. Furthermore, the programmer assumes encoding expansion will only expand a given character by a factor of 4, while the encoding of the ampersand expands by 5. As a result, when the encoding procedure expands the string it is possible to overflow the destination buffer if the attacker provides a string of many ampersands.
Example 3
The following example asks a user for an offset into an array to select an item.
(bad code)
Example Language: C
int main (int argc, char **argv) {
char *items[] = {"boat", "car", "truck", "train"};
int index = GetUntrustedOffset();
printf("You selected %s\n", items[index-1]);
}
The programmer allows the user to specify which element in the list to select, however an attacker can provide an out-of-bounds offset, resulting in a buffer over-read (CWE-126).
Example 4
In the following code, the method retrieves a value from an array at a specific array index location that is given as an input parameter to the method
(bad code)
Example Language: C
int getValueFromArray(int *array, int len, int index) {
int value;
// check that the array index is less than the maximum
// length of the array
if (index < len) {
// get the value at the specified index of the array
value = array[index];
}
// if array index is invalid then output error message
// and return value indicating error
else {
printf("Value is: %d\n", array[index]);
value = -1;
}
return value;
}
However, this method only verifies that the given array index is less than the maximum length of the array but does not check for the minimum value (CWE-839). This will allow a negative value to be accepted as the input array index, which will result in reading data before the beginning of the buffer (CWE-127) and may allow access to sensitive memory. The input array index should be checked to verify that is within the maximum and minimum range required for the array (CWE-129). In this example the if statement should be modified to include a minimum range check, as shown below.
(good code)
Example Language: C
...
// check that the array index is within the correct
// range of values for the array
if (index >= 0 && index < len) {
...
Example 5
Windows provides the _mbs family of functions to perform various operations on multibyte strings. When these functions are passed a malformed multibyte string, such as a string containing a valid leading byte followed by a single null byte, they can read or write past the end of the string buffer causing a buffer overflow. The following functions all pose a risk of buffer overflow: _mbsinc _mbsdec _mbsncat _mbsncpy _mbsnextc _mbsnset _mbsrev _mbsset _mbsstr _mbstok _mbccpy _mbslen
 Selected Observed
Examples
Selected Observed
Examples
Note: this is a curated list of examples for users to understand the variety of ways in which this weakness can be introduced. It is not a complete list of all CVEs that are related to this CWE entry.
| Reference | Description |
|---|---|
|
Incorrect URI normalization in application traffic product leads to buffer overflow, as exploited in the wild per CISA KEV. |
|
|
Buffer overflow in Wi-Fi router web interface, as exploited in the wild per CISA KEV. |
|
|
Classic stack-based buffer overflow in media player using a long entry in a playlist |
|
|
Heap-based buffer overflow in media player using a long entry in a playlist |
|
|
large precision value in a format string triggers overflow |
|
|
negative offset value leads to out-of-bounds read |
|
|
malformed inputs cause accesses of uninitialized or previously-deleted objects, leading to memory corruption |
|
|
chain: lack of synchronization leads to memory corruption |
|
|
Chain: machine-learning product can have a heap-based buffer overflow (CWE-122) when some integer-oriented bounds are calculated by using ceiling() and floor() on floating point values (CWE-1339) |
|
|
attacker-controlled array index leads to code execution |
|
|
chain: -1 value from a function call was intended to indicate an error, but is used as an array index instead. |
|
|
chain: incorrect calculations lead to incorrect pointer dereference and memory corruption |
|
|
product accepts crafted messages that lead to a dereference of an arbitrary pointer |
|
|
chain: malformed input causes dereference of uninitialized memory |
|
|
OS kernel trusts userland-supplied length value, allowing reading of sensitive information |
|
|
Chain: integer overflow in securely-coded mail program leads to buffer overflow. In 2005, this was regarded as unrealistic to exploit, but in 2020, it was rediscovered to be easier to exploit due to evolutions of the technology. |
|
|
buffer overflow involving a regular expression with a large number of captures |
|
|
chain: unchecked message size metadata allows integer overflow (CWE-190) leading to buffer overflow (CWE-119). |
 Weakness Ordinalities
Weakness Ordinalities
| Ordinality | Description |
|---|---|
|
Primary |
(where the weakness exists independent of other weaknesses) |
|
Resultant |
(where the weakness is typically related to the presence of some other weaknesses) |