CWE - CWE-416: Use After Free (4.19.1)
Weakness ID: 416
Vulnerability Mapping: ALLOWED This CWE ID may be used to map to real-world vulnerabilitiesAbstraction: Variant Variant - a weakness that is linked to a certain type of product, typically involving a specific language or technology. More specific than a Base weakness. Variant level weaknesses typically describe issues in terms of 3 to 5 of the following dimensions: behavior, property, technology, language, and resource.
 Description
Description
 Alternate Terms
Alternate Terms
| Dangling pointer |
a pointer that no longer points to valid memory, often after it has been freed |
| UAF |
commonly used acronym for Use After Free |
| Use-After-Free |
 Common Consequences
Common Consequences
 This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
| Impact | Details |
|---|---|
|
Modify Memory |
Scope: Integrity
The use of previously freed memory may corrupt valid data, if the memory area in question has been allocated and used properly elsewhere. |
|
DoS: Crash, Exit, or Restart |
Scope: Availability
If chunk consolidation occurs after the use of previously freed data, the process may crash when invalid data is used as chunk information. |
|
Execute Unauthorized Code or Commands |
Scope: Integrity, Confidentiality, Availability
If malicious data is entered before chunk consolidation can take place, it may be possible to take advantage of a write-what-where primitive to execute arbitrary code. If the newly allocated data happens to hold a class, in C++ for example, various function pointers may be scattered within the heap data. If one of these function pointers is overwritten with an address to valid shellcode, execution of arbitrary code can be achieved. |
 Potential Mitigations
Potential Mitigations
| Phase(s) | Mitigation |
|---|---|
|
Architecture and Design |
Strategy: Language Selection Choose a language that provides automatic memory management. |
|
Implementation |
Strategy: Attack Surface Reduction When freeing pointers, be sure to set them to NULL once they are freed. However, the utilization of multiple or complex data structures may lower the usefulness of this strategy. Effectiveness: Defense in Depth Note: If a bug causes an attempted access of this pointer, then a NULL dereference could still lead to a crash or other unexpected behavior, but it will reduce or eliminate the risk of code execution. |
 Relationships
Relationships
 This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
 Relevant to the view "Research Concepts" (View-1000)
Relevant to the view "Research Concepts" (View-1000)
| Nature | Type | ID | Name |
|---|---|---|---|
| ChildOf |
|
825 | Expired Pointer Dereference |
| PeerOf |
|
415 | Double Free |
| CanFollow |
|
362 | Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') |
| CanFollow |
|
364 | Signal Handler Race Condition |
| CanFollow |
|
754 | Improper Check for Unusual or Exceptional Conditions |
| CanFollow |
|
1265 | Unintended Reentrant Invocation of Non-reentrant Code Via Nested Calls |
| CanPrecede |
|
120 | Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') |
| CanPrecede |
|
123 | Write-what-where Condition |
 Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
| Nature | Type | ID | Name |
|---|---|---|---|
| ChildOf |
|
672 | Operation on a Resource after Expiration or Release |
 Relevant to the view "CISQ Quality Measures (2020)" (View-1305)
Relevant to the view "CISQ Quality Measures (2020)" (View-1305)
| Nature | Type | ID | Name |
|---|---|---|---|
| ChildOf |
|
672 | Operation on a Resource after Expiration or Release |
 Relevant to the view "CISQ Data Protection Measures" (View-1340)
Relevant to the view "CISQ Data Protection Measures" (View-1340)
| Nature | Type | ID | Name |
|---|---|---|---|
| ChildOf |
|
672 | Operation on a Resource after Expiration or Release |
 Modes
Of Introduction
Modes
Of Introduction
 The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
| Phase | Note |
|---|---|
| Implementation |
 Applicable Platforms
Applicable Platforms
 This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
| Languages |
Class: Memory-Unsafe (Often Prevalent) C (Often Prevalent) C++ (Often Prevalent) |
 Likelihood Of Exploit
Likelihood Of Exploit
 Demonstrative Examples
Demonstrative Examples
Example 1
The following example demonstrates the weakness.
(bad code)
Example Language: C
#include <stdio.h>
#include <unistd.h>
#define BUFSIZER1 512
#define BUFSIZER2 ((BUFSIZER1/2) - 8)
int main(int argc, char **argv) {
char *buf1R1;
char *buf2R1;
char *buf2R2;
char *buf3R2;
buf1R1 = (char *) malloc(BUFSIZER1);
buf2R1 = (char *) malloc(BUFSIZER1);
free(buf2R1);
buf2R2 = (char *) malloc(BUFSIZER2);
buf3R2 = (char *) malloc(BUFSIZER2);
strncpy(buf2R1, argv[1], BUFSIZER1-1);
free(buf1R1);
free(buf2R2);
free(buf3R2);
}
Example 2
The following code illustrates a use after free error:
(bad code)
Example Language: C
char* ptr = (char*)malloc (SIZE);
if (err) {
abrt = 1;
free(ptr);
}
...
if (abrt) {
logError("operation aborted before commit", ptr);
}
When an error occurs, the pointer is immediately freed. However, this pointer is later incorrectly used in the logError function.
 Selected Observed
Examples
Selected Observed
Examples
Note: this is a curated list of examples for users to understand the variety of ways in which this weakness can be introduced. It is not a complete list of all CVEs that are related to this CWE entry.
| Reference | Description |
|---|---|
|
Chain: an operating system kernel has insufficent resource locking (CWE-413) leading to a use after free (CWE-416). |
|
|
Chain: two threads in a web browser use the same resource (CWE-366), but one of those threads can destroy the resource before the other has completed (CWE-416). |
|
|
Chain: mobile platform race condition (CWE-362) leading to use-after-free (CWE-416), as exploited in the wild per CISA KEV. |
|
|
Chain: race condition (CWE-362) leads to use-after-free (CWE-416), as exploited in the wild per CISA KEV. |
|
|
Use-after-free triggered by closing a connection while data is still being transmitted. |
|
|
Improper allocation for invalid data leads to use-after-free. |
|
|
certificate with a large number of Subject Alternate Names not properly handled in realloc, leading to use-after-free |
|
|
Timers are not disabled when a related object is deleted |
|
|
Access to a "dead" object that is being cleaned up |
|
|
object is deleted even with a non-zero reference count, and later accessed |
|
|
use-after-free involving request containing an invalid version number |
|
|
unload of an object that is currently being accessed by other functionality |
|
|
incorrectly tracking a reference count leads to use-after-free |
|
|
use-after-free related to use of uninitialized memory |
|
|
HTML document with incorrectly-nested tags |
|
|
Use after free in ActiveX object by providing a malformed argument to a method |
|
|
use-after-free by disconnecting during data transfer, or a message containing incorrect data types |
|
|
disconnect during a large data transfer causes incorrect reference count, leading to use-after-free |
|
|
use-after-free found by fuzzing |
|
|
Chain: race condition (CWE-362) from improper handling of a page transition in web client while an applet is loading (CWE-368) leads to use after free (CWE-416) |
|
|
realloc generates new buffer and pointer, but previous pointer is still retained, leading to use after free |
|
|
Use-after-free in web browser, probably resultant from not initializing memory. |
|
|
use-after-free when one thread accessed memory that was freed by another thread |
|
|
assignment of malformed values to certain properties triggers use after free |
|
|
mail server does not properly handle a long header. |
|
|
chain: integer overflow leads to use-after-free |
|
|
freed pointer dereference |
|
|
Chain: A multi-threaded race condition (CWE-367) allows attackers to cause two threads to process the same RPC request, which causes a use-after-free (CWE-416) in one thread |
 Weakness Ordinalities
Weakness Ordinalities
| Ordinality | Description |
|---|---|
|
Resultant |
(where the weakness is typically related to the presence of some other weaknesses) If the product accesses a previously-freed pointer, then it means that a separate weakness or error already occurred previously, such as a race condition, an unexpected or poorly handled error condition, confusion over which part of the program is responsible for freeing the memory, performing the free too soon, etc. |
 Detection
Methods
Detection
Methods
| Method | Details |
|---|---|
|
Fuzzing |
Fuzz testing (fuzzing) is a powerful technique for generating large numbers of diverse inputs - either randomly or algorithmically - and dynamically invoking the code with those inputs. Even with random inputs, it is often capable of generating unexpected results such as crashes, memory corruption, or resource consumption. Fuzzing effectively produces repeatable test cases that clearly indicate bugs, which helps developers to diagnose the issues. Effectiveness: High |
|
Automated Static Analysis |
Automated static analysis, commonly referred to as Static Application Security Testing (SAST), can find some instances of this weakness by analyzing source code (or binary/compiled code) without having to execute it. Typically, this is done by building a model of data flow and control flow, then searching for potentially-vulnerable patterns that connect "sources" (origins of input) with "sinks" (destinations where the data interacts with external components, a lower layer such as the OS, etc.) Effectiveness: High |
|
Automated Dynamic Analysis |
Use tools that are integrated during compilation to insert runtime error-checking mechanisms related to memory safety errors, such as AddressSanitizer (ASan) for C/C++ [REF-1518]. Effectiveness: Moderate Note:Crafted inputs are necessary to reach the code containing the error, such as generated by fuzzers. Also, these tools may reduce performance, and they only report the error condition - not the original mistake that led to the error. |
 Functional Areas
Functional Areas
- Memory Management
 Affected Resources
Affected Resources
- Memory
 Memberships
Memberships
 This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
 Vulnerability Mapping Notes
Vulnerability Mapping Notes
| Usage |
ALLOWED
(this CWE ID may be used to map to real-world vulnerabilities) |
| Reason | Acceptable-Use |
|
Rationale |
This CWE entry is at the Variant level of abstraction, which is a preferred level of abstraction for mapping to the root causes of vulnerabilities. |
|
Comments |
Carefully read both the name and description to ensure that this mapping is an appropriate fit. Do not try to 'force' a mapping to a lower-level Base/Variant simply to comply with this preferred level of abstraction. |
 Taxonomy
Mappings
Taxonomy
Mappings
| Mapped Taxonomy Name | Node ID | Fit | Mapped Node Name |
|---|---|---|---|
| ISA/IEC 62443 | Part 4-1 | Req SI-1 | |
| 7 Pernicious Kingdoms | Use After Free | ||
| CLASP | Using freed memory | ||
| CERT C Secure Coding | MEM00-C | Allocate and free memory in the same module, at the same level of abstraction | |
| CERT C Secure Coding | MEM01-C | Store a new value in pointers immediately after free() | |
| CERT C Secure Coding | MEM30-C | Exact | Do not access freed memory |
| Software Fault Patterns | SFP15 | Faulty Resource Use |
 References
References
 Content
History
Content
History
 Submissions Submissions |
||
|---|---|---|
| Submission Date | Submitter | Organization |
|
2006-07-19
(CWE Draft 3, 2006-07-19) |
7 Pernicious Kingdoms | |
 Contributions Contributions |
||
| Contribution Date | Contributor | Organization |
| 2022-06-28 | Anonymous External Contributor | |
| Suggested rephrase for extended description | ||
|
2023-11-14
(CWE 4.14, 2024-02-29) |
participants in the CWE ICS/OT SIG 62443 Mapping Fall Workshop | |
| Contributed or reviewed taxonomy mappings for ISA/IEC 62443 | ||
|
2024-02-29
(CWE 4.15, 2024-07-16) |
Abhi Balakrishnan | |
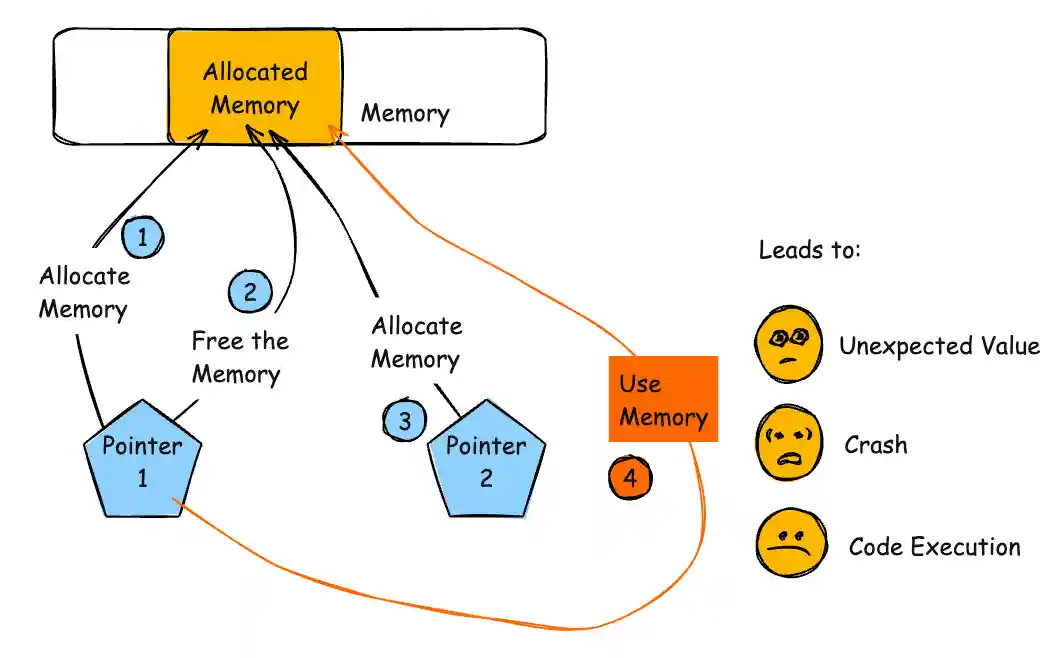
| Provided diagram to improve CWE usability | ||
 Modifications Modifications |
||
| Modification Date | Modifier | Organization |
|
2025-12-11
(CWE 4.19, 2025-12-11) |
CWE Content Team | MITRE |
| updated Applicable_Platforms, Detection_Factors, References, Relationships | ||
|
2025-09-09
(CWE 4.18, 2025-09-09) |
CWE Content Team | MITRE |
| updated Functional_Areas | ||
|
2025-04-03
(CWE 4.17, 2025-04-03) |
CWE Content Team | MITRE |
| updated Observed_Examples | ||
|
2024-11-19
(CWE 4.16, 2024-11-19) |
CWE Content Team | MITRE |
| updated Relationships | ||
|
2024-07-16
(CWE 4.15, 2024-07-16) |
CWE Content Team | MITRE |
| updated Alternate_Terms, Common_Consequences, Description, Diagram, Potential_Mitigations, Relationships, Weakness_Ordinalities | ||
|
2024-02-29
(CWE 4.14, 2024-02-29) |
CWE Content Team | MITRE |
| updated Taxonomy_Mappings | ||
| 2023-10-26 | CWE Content Team | MITRE |
| updated Observed_Examples | ||
| 2023-06-29 | CWE Content Team | MITRE |
| updated Mapping_Notes, Relationships | ||
| 2023-04-27 | CWE Content Team | MITRE |
| updated Detection_Factors, Relationships, Time_of_Introduction | ||
| 2022-10-13 | CWE Content Team | MITRE |
| updated Description, Relationships, Taxonomy_Mappings | ||
| 2022-06-28 | CWE Content Team | MITRE |
| updated Observed_Examples, Relationships | ||
| 2021-07-20 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2020-12-10 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2020-08-20 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2020-06-25 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2020-02-24 | CWE Content Team | MITRE |
| updated References, Relationships, Taxonomy_Mappings | ||
| 2019-09-19 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2019-06-20 | CWE Content Team | MITRE |
| updated Relationships, Type | ||
| 2019-01-03 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2017-11-08 | CWE Content Team | MITRE |
| updated Demonstrative_Examples, Relationships, Taxonomy_Mappings, White_Box_Definitions | ||
| 2015-12-07 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2014-07-30 | CWE Content Team | MITRE |
| updated Relationships, Taxonomy_Mappings | ||
| 2012-05-11 | CWE Content Team | MITRE |
| updated References, Relationships | ||
| 2011-09-13 | CWE Content Team | MITRE |
| updated Relationships, Taxonomy_Mappings | ||
| 2011-06-27 | CWE Content Team | MITRE |
| updated Demonstrative_Examples | ||
| 2011-06-01 | CWE Content Team | MITRE |
| updated Common_Consequences | ||
| 2011-03-29 | CWE Content Team | MITRE |
| updated Description | ||
| 2010-12-13 | CWE Content Team | MITRE |
| updated Alternate_Terms, Common_Consequences, Description, Observed_Examples, Other_Notes, Potential_Mitigations, Relationships | ||
| 2010-09-27 | CWE Content Team | MITRE |
| updated Observed_Examples, Relationships | ||
| 2010-06-21 | CWE Content Team | MITRE |
| updated Potential_Mitigations | ||
| 2010-02-16 | CWE Content Team | MITRE |
| updated Relationships | ||
| 2009-10-29 | CWE Content Team | MITRE |
| updated Common_Consequences | ||
| 2009-05-27 | CWE Content Team | MITRE |
| updated Demonstrative_Examples | ||
| 2009-03-10 | CWE Content Team | MITRE |
| updated Demonstrative_Examples | ||
| 2008-11-24 | CWE Content Team | MITRE |
| updated Relationships, Taxonomy_Mappings | ||
| 2008-09-08 | CWE Content Team | MITRE |
| updated Applicable_Platforms, Common_Consequences, Relationships, Observed_Example, Other_Notes, Taxonomy_Mappings | ||
| 2008-08-01 | KDM Analytics | |
| added/updated white box definitions | ||
| 2008-07-01 | Eric Dalci | Cigital |
| updated Potential_Mitigations, Time_of_Introduction | ||