The ultimate Android RE experience right inside your VS Code.
APKLab seamlessly integrates the best open-source tools: Apktool, smali-lsp, Jadx, uber-apk-signer, apk-mitm and more to the excellent VS Code so you can focus on app analysis and get it done without leaving the IDE.
Features
- Decode/Edit/Rebuild app resource files
- Disassemble/Mod/Rebuild an APK to/from Smali
- Decompile the APK to Java source
- Excellent Smali language support with smali-lsp — go to definition, find references, hover, call/type hierarchy, code lens, completion, diagnostics
- Analyze & mod effectively in VS Code with full IDE features
- Sign & Install the APK after rebuild
- Generate Frida hooks for any smali methods
- Inject Frida gadget into APK with automatic main activity patching
- Initialize
gitrepo in project dir to track changes - Apply MITM patch for HTTPS inspection
- Interactive Malware Analysis Report
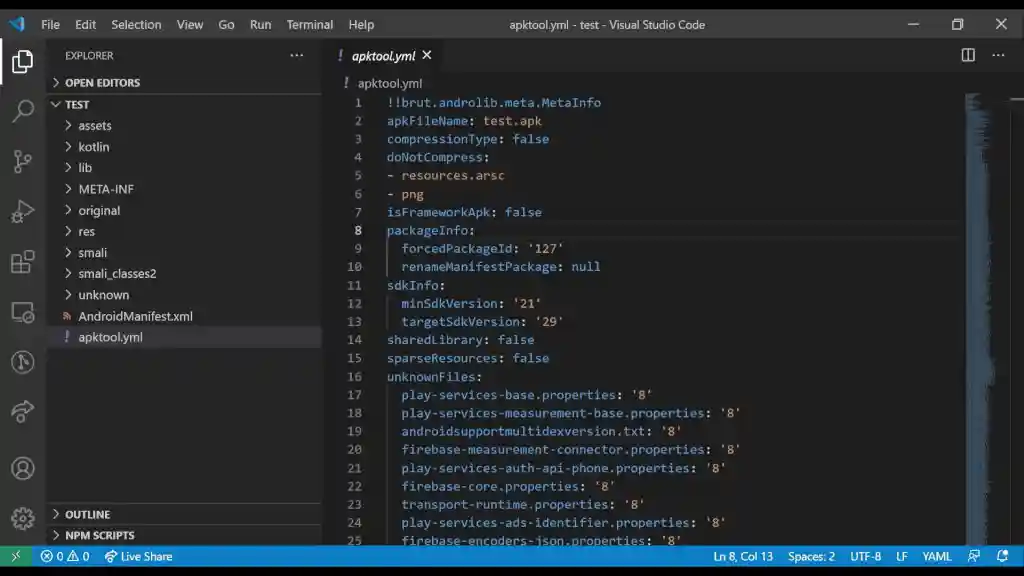
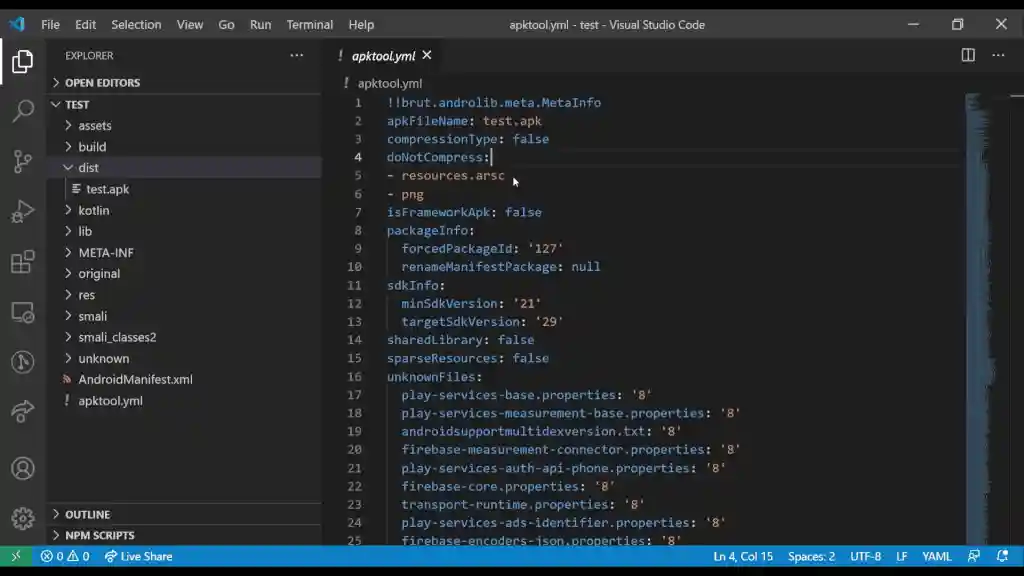
- Support for Apktool-style projects (
apktool.yml) - Support for Apktool 3.0+ CLI arguments
- Android resource frameworks management
- Support for user-provided keystore for APK signing
- Check for update and install needed tools automatically
- Supports Linux, Mac and WSL2
Requirements
-
JDK 17+
Run
java -versionin your Shell, if not found, download from here. -
quark-engine >=21.01.6 (optional - for malware analysis)
Run
quarkin your Shell, if not found, check official docs. -
adb (optional)
Run
adb devicesin your Shell, if not found, check this guide.
Getting Started
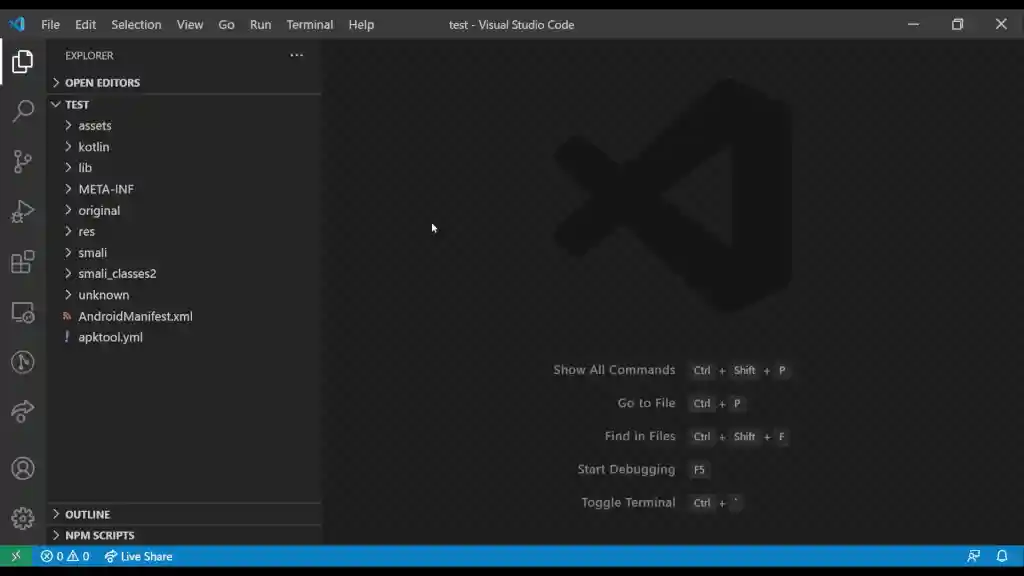
Open APK or Apktool project
-
Open the Command Palette (Ctrl+Shift+P) ➜ APKLab: Open an APK
-
Or Just open an existing Apktool project folder
Apply MITM patch
ReBuild and Sign APK
Install APK to device
Generate Frida Hook
- Right-Click inside a
.methodin a.smalifile ➜ APKLab: Generate Frida Hook - Hook is appended to
frida_hooks.tsin the project root
Inject Frida Gadget
- Right-Click on or inside
apktool.ymlfile ➜ APKLab: Inject Frida Gadget - Select the gadget
.sofile, target architecture, and the main activity is patched automatically
Clean ApkTool frameworks dir
- Open the Command Palette (Ctrl+Shift+P) ➜ APKLab: Empty ApkTool Framework Dir
Extension Settings
Dependency Paths
-
apklab.apktoolPath: Full Path ofapktool.jar. If you want to use a different version of it, change it like:"apklab.apktoolPath": "/home/oozer/downloads/apktool_2.4.1.jar" -
apklab.apkSignerPath: Full Path ofuber-apk-signer.jar. If you want to use a different version of it, change it like:"apklab.apkSignerPath": "/home/oozer/downloads/uber-apk-signer-1.1.0.jar" -
apklab.jadxDirPath: Full Path ofjadx-x.y.zdir. If you want to use a different version of it, change it like:"apklab.jadxDirPath": "/home/oozer/downloads/jadx-1.1.0" -
apklab.smaliLspPath: Full Path ofsmali-lsp.jar. If you want to use a different version of it, change it like:"apklab.smaliLspPath": "/home/oozer/downloads/smali-lsp.jar" -
apklab.javaPath: Path to the Java executable (default:java). Change it if Java is not on your PATH:"apklab.javaPath": "/usr/lib/jvm/java-17/bin/java"
Keystore configuration
-
apklab.keystorePath: Put the absolute path of your Java keystore(.jksor.keystore) file here."apklab.keystorePath": "/home/oozer/downloads/debug.keystore" -
apklab.keystorePassword: Put the password of your keystore here. -
apklab.keyAlias: Put the alias of the used key in the keystore here. -
apklab.keyPassword: Put the password of the used key in the keystore here.
Additional configuration
apklab.initProjectDirAsGit: Initialize project output directory as Git repository.apklab.updateTools: Whether APKLab should check for tools (for apklab, jadx...) update and show a notification.smaliLsp.trace.server: Traces the communication between VS Code and the Smali Language Server (off,messages,verbose).
Known Issues
Please check our Bug tracker for known issues.
Contribution Guide
For bug reports, feature requests or simply discussing an idea, please open an issue here. PRs are always welcome.
Changelog
Credits
Details
- Feimaomii for the awesome logo
- Aman Sharma for active contribution
- Niklas Higi for apk-mitm
- Shaun Dang, JunWei Song & KunYu Chen for Quark-Engine
- iBotPeaches, brutall and JesusFreke for Apktool & Smali
- patrickfav for uber-apk-signer
- skylot for Jadx