Splunk Attack Range
Purpose
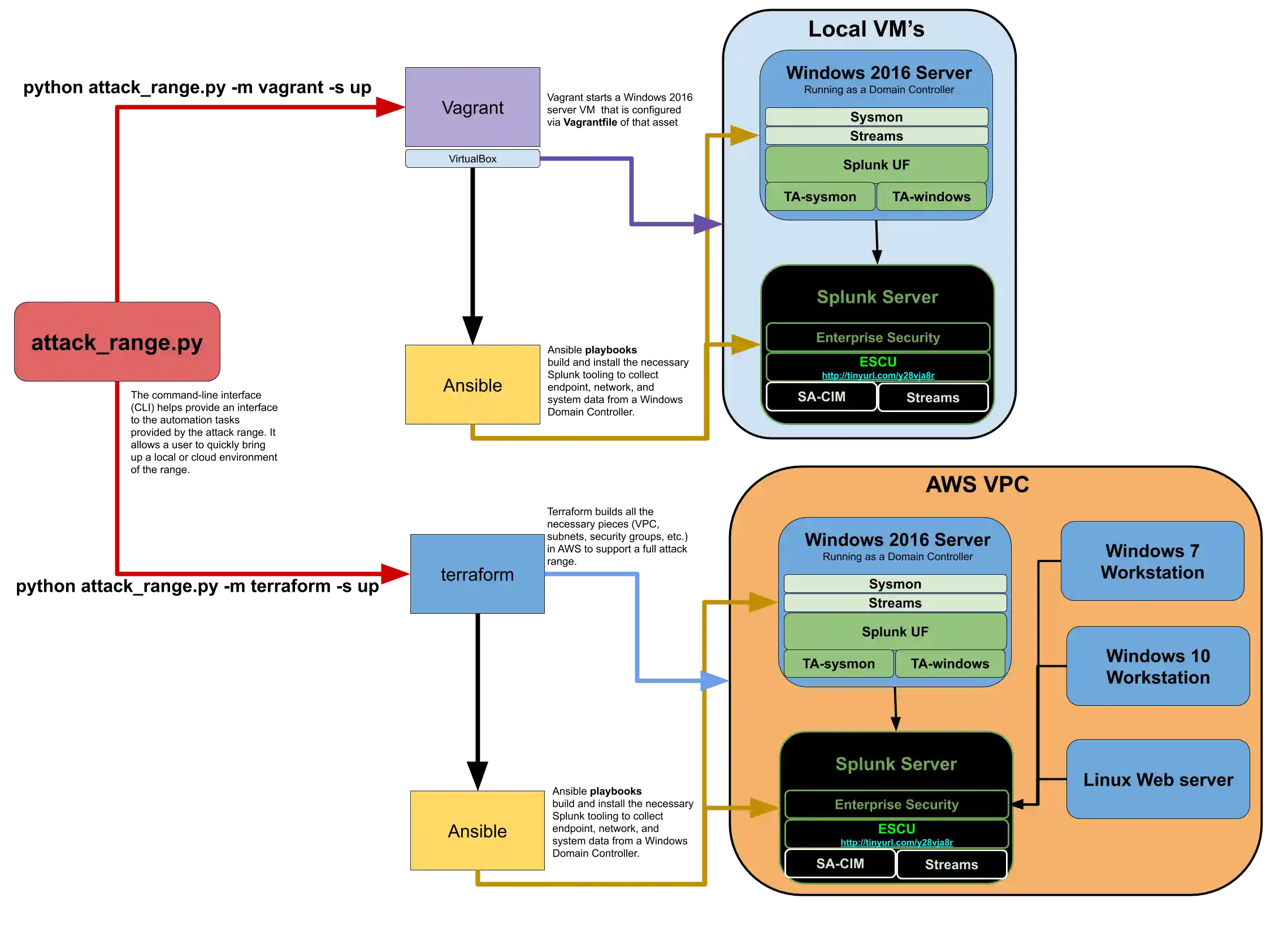
This framework allows the security analyst to quickly and repeatedly replicate and generate data as close to "ground truth" as possible, in a format that allows the creation of detections, investigations, knowledge objects, and playbooks in Splunk.
The data includes logs, network captures, endpoint events, and so on, derived from either known attack-simulation engines (Atomic Red Team/AttackIQ) or recent exploit code on local (Vagrant) or cloud enviroments (Terraform). Inspired by DetectionLab.
Architecture
Usage
usage: attack_range.py [-h] [-b APPBIN] -m MODE -s STATE [-v VERSION]
[-vbox VAGRANT_BOX] [-vls] [-se SIMULATION_ENGINE]
starts a attack range ready to collect attack data into Splunk
optional arguments:
-h, --help show this help message and exit
-b APPBIN, --appbin APPBIN
directory to store binaries in
-m MODE, --mode MODE mode of operation, Terraform/Vagrant, please see
configuration for each at:
https://github.com/splunk/attack_range
-s STATE, --state STATE
state of the range, defaults to "up", up/down allowed
-v VERSION, --version VERSION
shows current attack_range version
-vbox VAGRANT_BOX, --vagrant_box VAGRANT_BOX
select the individual Vagrant box to stand up or destroy
-vls, --vagrant_list prints out all avaiable vagrant boxes
-se SIMULATION_ENGINE, --simulation_engine SIMULATION_ENGINE
please select a simulation engine; defaults to
"atomic_red_team"
Running
git clone https://github.com/splunk/attack_range && cd attack_rangeclone project and cd into the project dirvirtualenv -p python3 venv && source venv/bin/activate && pip install -r requirements.txtcreate virtualenv and install requirementspython attack_range.py --state up --mode vagrantstart up a range locally using vagrant orpython attack_range.py --state up --mode terraformto deploy it to "the cloud"
See Usage for more options, make sure that you configure the mode first
If you are on OSX, you will have to install sshpass brew install https://raw.githubusercontent.com/kadwanev/bigboybrew/master/Library/Formula/sshpass.rb
Configure
For Terraform
brew install terraforminstall Terraform CLI on OSX other platformsbrew install awscliinstall AWS CLI on OSX otherwise see: guide- Get AWS API token
aws configure - Set Terraform variables under terraform/terraform.tfvars
For Vagrant
brew cask install virtualboxif you don't already have virtual box installed on OSX, otherwise see their installation instructions.brew cask install vagrantinstall Vagrant CLI on OSX, otherwise see: guide
Range Settings
To configure general range settings like your Splunk server default username, sysmon template to deploy, or Active Directory admin creds, edit: ansible/vars/vars.yml
Developing
- Create virtualenv and install requirements:
virtualenv -p python3 venv && source venv/bin/activate && pip install -r requirements.txt - Install pre-commit hooks
pre-commit install - Install Ansible on OSX
brew install ansible
Support
You can get help with setting up your own attack range in the Splunk Community Slack under the #security-research channel.
Author
Contributors
- Rod Soto
- Bhavin Patel
- Russ Nolen
To Dos
- Implement Atomic Red Team simulation engine execution
- Implement Attack IQ simulation engine execution
- Create global .conf file