Cartography is a Python tool that pulls infrastructure assets and their relationships into a Neo4j graph database.
What it connects: AWS, GCP, Azure, Kubernetes, GitHub, Okta, Entra ID, CrowdStrike, and 30+ more platforms.
Questions it answers:
- Which identities have access to which datastores? How about across multiple tenants, or providers?
- Am I affected by any critical vulnerabilities or compromised software packages?
- What are the network paths in and out of my environment?
- Which compute instances are exposed to the internet?
- What AI agents are running in production, and what permissions do they have?
Quick Start
Install Cartography
Start Neo4j database
docker run -d --publish=7474:7474 --publish=7687:7687 -v data:/data --env=NEO4J_AUTH=none neo4j:5-community
Confirm that http://localhost:7474 is up.
Sync your first data source (AWS example)
Ensure your AWS credentials and default region are configured (e.g. via AWS_PROFILE, AWS_DEFAULT_REGION, or ~/.aws/config). See AWS credentials docs for reference.
Run Cartography:
cartography --neo4j-uri bolt://localhost:7687 --selected-modules aws
See the full install guide for other platforms.
Query the graph
Open http://localhost:7474 and try:
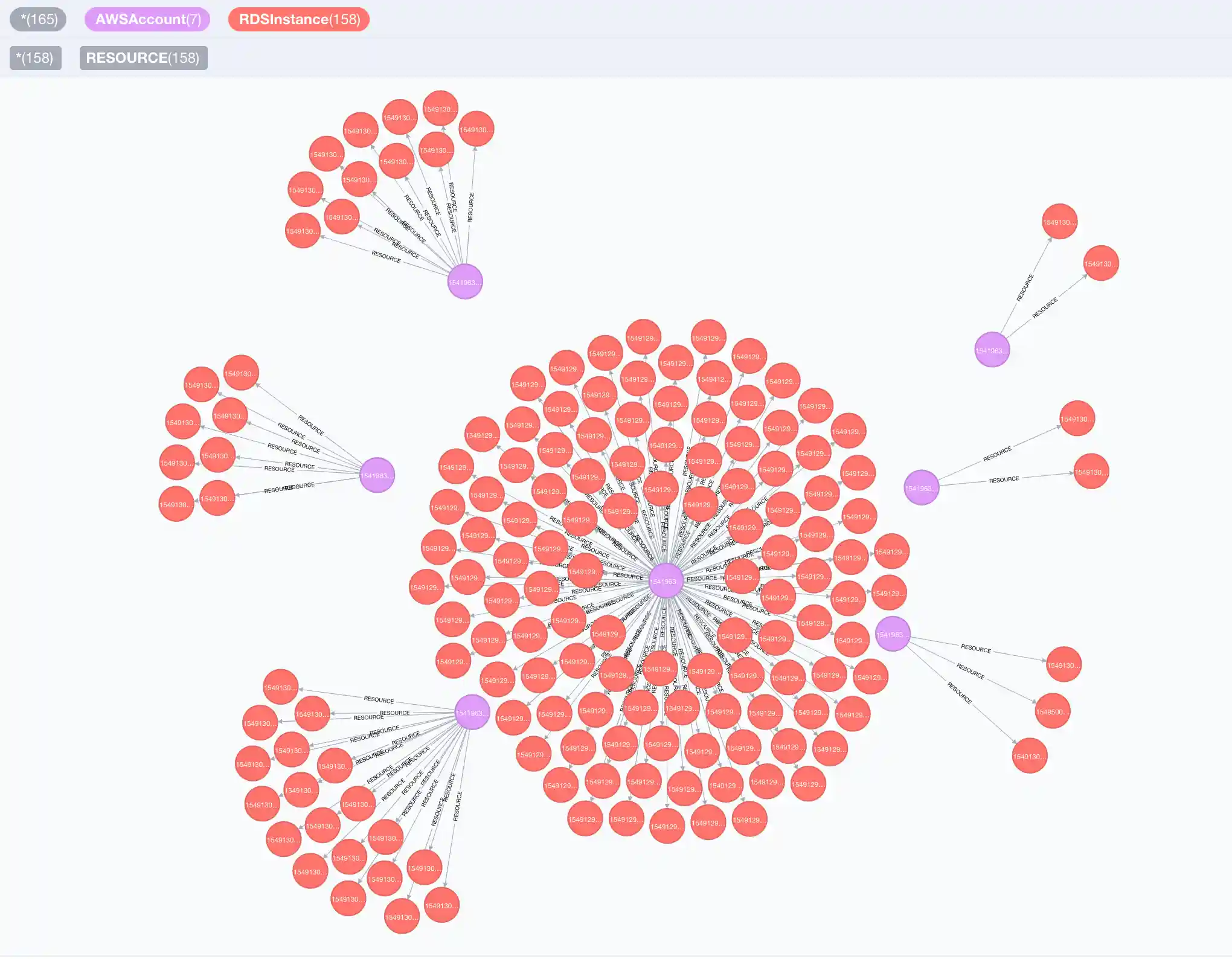
// Find unencrypted RDS instances by account MATCH (a:AWSAccount)-[:RESOURCE]->(rds:RDSInstance{storage_encrypted:false}) RETURN a.name, rds.id
// Find EC2 instances exposed to the internet MATCH (instance:EC2Instance{exposed_internet: true}) RETURN instance.instanceid, instance.publicdnsname
See the querying tutorial and data schema for more use-cases.
Run security rules
Check your environment against common security frameworks:
cartography-rules run all
See the rules docs for more detail.
Supported platforms
Click to expand full list of 30+ supported platforms
- Airbyte - Organization, Workspace, User, Source, Destination, Connection, Tag, Stream
- Amazon Web Services - ACM, API Gateway, Bedrock, CloudWatch, CodeBuild, Config, Cognito, EC2, ECS, ECR (including multi-arch images, image layers, and attestations), EFS, Elasticsearch, Elastic Kubernetes Service (EKS), DynamoDB, Glue, GuardDuty, IAM, Inspector, KMS, Lambda, RDS, Redshift, Route53, S3, SageMaker, Secrets Manager(Secret Versions), Security Hub, SNS, SQS, SSM, STS, Tags
- AIBOM - AI component detections linked to ECR images
- Anthropic - Organization, ApiKey, User, Workspace
- BigFix - Computers
- Cloudflare - Account, Role, Member, Zone, DNSRecord
- Crowdstrike Falcon - Hosts, Spotlight vulnerabilities, CVEs
- DigitalOcean
- Duo - Users, Groups, Endpoints
- GitHub - repos, branches, users, teams, dependency graph manifests, dependencies
- Google Cloud Platform - Artifact Registry, Bigtable, Cloud Functions, Cloud Resource Manager, Cloud Run, Cloud SQL, Compute, DNS, IAM, KMS, Secret Manager, Storage, Google Kubernetes Engine, Vertex AI
- Google Workspace - users, groups, devices, OAuth apps
- Jumpcloud
- Kandji - Devices
- Keycloak - Realms, Users, Groups, Roles, Scopes, Clients, IdentityProviders, Authentication Flows, Authentication Executions, Organizations, Organization Domains
- Kubernetes - Cluster, Namespace, Service, Pod, Container, ServiceAccount, Role, RoleBinding, ClusterRole, ClusterRoleBinding, OIDCProvider
- Lastpass - users
- Microsoft Azure - App Service, Container Instance, CosmosDB, Data Factory, Event Grid, Firewall, Firewall Policy, Functions, Key Vault, Azure Kubernetes Service (AKS), Load Balancer, Logic Apps, Resource Group, SQL, Storage, Virtual Machine, Virtual Networks
- Microsoft Entra ID - Users, Groups, Applications, OUs, App Roles, federation to AWS Identity Center
- NIST CVE - Common Vulnerabilities and Exposures (CVE) data from NIST database
- Okta - users, groups, organizations, roles, applications, factors, trusted origins, reply URIs, federation to AWS roles, federation to AWS Identity Center
- OpenAI - Organization, AdminApiKey, User, Project, ServiceAccount, ApiKey
- Oracle Cloud Infrastructure - IAM
- PagerDuty - Users, teams, services, schedules, escalation policies, integrations, vendors
- Scaleway - Projects, IAM, Local Storage, Instances
- SentinelOne - Accounts, Agents, Applications, Application Versions, CVEs
- Slack - Teams, Users, UserGroups, Channels
- SnipeIT - Users, Assets
- Spacelift - Accounts, Spaces,Users, Stacks, WorkerPools, Workers, Runs, GitCommits
- SubImage - Tenant, TeamMember, APIKey, Neo4jUser, Module, Framework
- Tailscale - Tailnet, Users, Devices, Groups, Tags, PostureIntegrations
- Trivy Scanner - AWS ECR Images
Community
- Join us on Slack: CNCF Slack in the
#cartographychannel. - Monthly community meeting — minutes · past recordings
Contributing
Thank you for considering contributing to Cartography!
All contributors and participants must follow the CNCF code of conduct.
Submit a GitHub issue to report a bug or request a new feature. Larger discussions happen in GitHub Discussions.
Get started with our developer documentation.
Who uses Cartography?
- Lyft
- Thought Machine
- MessageBird
- Cloudanix
- Corelight
- SubImage
- Superhuman
- {Your company here} :-)
If your organization uses Cartography, please file a PR and update this list. Say hi on Slack too!
License
This project is licensed under the Apache 2.0 License.
Cartography is a Cloud Native Computing Foundation sandbox project.