Scan and analyze GitHub repository with SonarQube Cloud
Note
SonarCloud got renamed to SonarQube Cloud
Setup
Automatic Analysis
Important
With Automatic Analysis for .NET, certain rules for .NET source code are automatically deactivated. This includes security rules, all rules that come from outside the Sonar Way quality profile, as well as certain rules from within it.
Note
Automatic analysis is only supported for GitHub repositories. If you are using a different version control system, you will need to use a different method to analyze your code.
- Follow the docs under SonarQube Cloud - Getting Started with GitHub to setup
SonarQube CloudwithGitHub- Sign up at SonarQube Cloud
- Click
Import another organization - Select your personal GitHub account or the organization that contains the repository you want to scan
- When reaching the
Create your SonarQube Cloud organizationpage adjust/update data and clickCreate organization - On
Analyze projectspage select the repository you want to scan and clickSet Up - On
Set up project for Clean as You Codepage select the desired code definition and clickCreate project
- After completing the setup, the repository will be scanned automatically and you will see the results on the
SonarQube Clouddashboard
CI-based analysis
Important
Assumption: Automatic analysis is already set up for the repository
To set up CI-based analysis with GitHub actions ...
- ... either follow the instructions (guided wizard) under https://sonarcloud.io/project/analysis_method?id=SONAR_CLOUD_PROJECT_ID
- ... or use the official sonarqube-scan-action
Tip
For an example usage of sonarqube-scan-action, see here
Include languages other than C#
To include i.e. terraform files in the analysis of SonarScanner for .NET, the following adjustments are required.
-
Extend the
dotnet-sonarscanner begincommand with project base dir argument/d:sonar.projectBaseDir="D:\a\GITHUB_PROJECT_NAME\GITHUB_PROJECT_NAME"whereGITHUB_PROJECT_NAMEis the name of the GitHub project -
Include the corresponding source files/folders in one of the projects
csprojfile<ItemGroup> <!-- This is required to include terraform files in SonarQube Cloud analysis --> <Content Include="..\..\deploy\**\*.tf" Visible="false"> <CopyToOutputDirectory>Never</CopyToOutputDirectory> </Content> </ItemGroup>
For more details see here
Include .NET test coverage
To include .NET test coverage in the analysis of SonarScanner for .NET, the following adjustments are required in the GitHub actions workflow (see .github\workflows\quality.yml).
# Install dotnet-coverage - name: Install dotnet-coverage shell: pwsh run: | dotnet tool install --global dotnet-coverage - name: Build and analyze env: GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }} # Needed to get PR information, if any SONAR_TOKEN: ${{ secrets.SONAR_TOKEN }} shell: pwsh run: | $ErrorActionPreference = "Stop" $PSNativeCommandUseErrorActionPreference = $true # Add /d:sonar.cs.vscoveragexml.reportsPaths=coverage.xml ${{ runner.temp }}\scanner\dotnet-sonarscanner begin /k:"rufer7_github-sonarcloud-integration" /o:"rufer7" /d:sonar.token="$env:SONAR_TOKEN" /d:sonar.host.url="https://sonarcloud.io" /d:sonar.projectBaseDir="D:\a\github-sonarcloud-integration\github-sonarcloud-integration" /d:sonar.cs.vscoveragexml.reportsPaths=coverage.xml /d:sonar.terraform.provider.azure.version=3.100.0 dotnet build .\src\ArbitrarySolution.sln --configuration Release # Execute tests and collect coverage dotnet-coverage collect 'dotnet test .\src\ArbitraryProject.Tests\ArbitraryProject.Tests.csproj' -f xml -o 'coverage.xml' ${{ runner.temp }}\scanner\dotnet-sonarscanner end /d:sonar.token="$env:SONAR_TOKEN"
Scan Results
SonarQube Cloud
The scan results can be viewed on the SonarQube Cloud dashboard
GitHub
Important
The new SonarQube Cloud plans Free and Team do not support GitHub Advanced Security integration anymore - only Enterprise plan does
For more details, see here
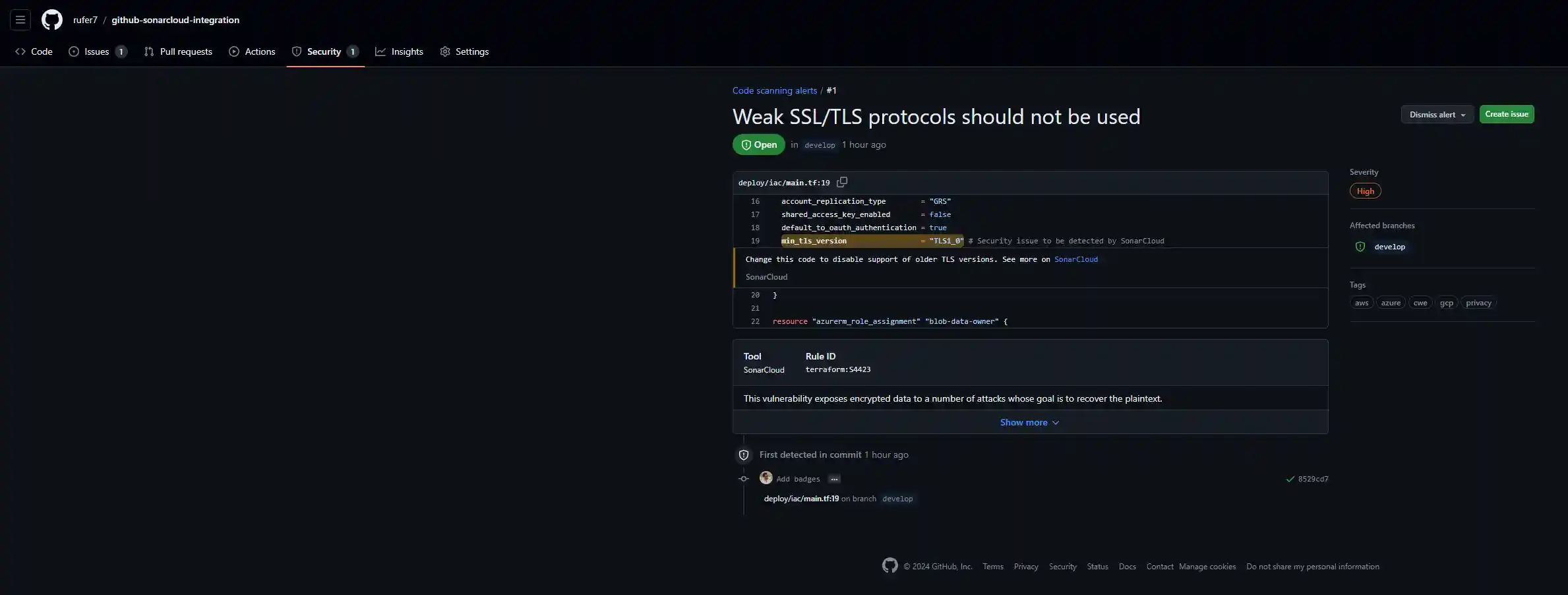
Security hotspots detected by SonarQube Cloud can be viewed directly on the GitHub repository under Security tab in the Code scanning section
Example
Pull Request (GitHub)
Pull request analysis results can be found directly on the pull requests.
For an example, see here